LetsEncrypt Support for openSUSE
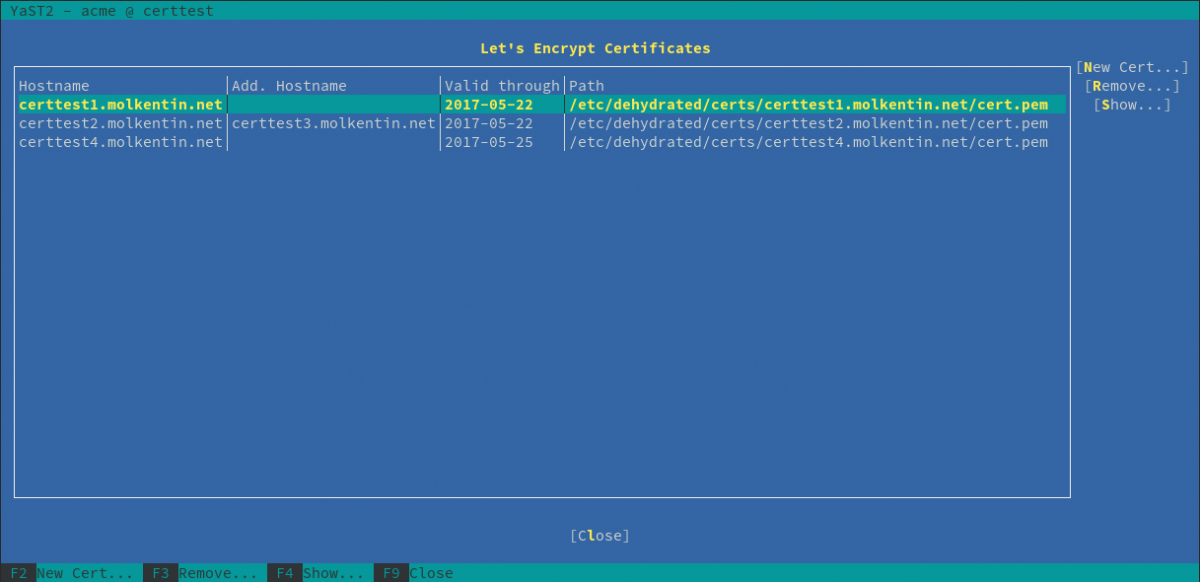
For my first hackweek, I joined forces with Klaas to work on a LetsEncrypt integration for openSUSE. So we went to create yast-acme. Too many acronyms already? Alright, let’s start with… The Elevator Pitch “Imagine setting up encrypted websites and …